Often when we find a vulnerability or missconfiguration in the system itself, we will thought it was a small thing, because we respond not as a security hole. Tools and techniques used are mostly variations of crackers that attack them did before. For both system and network administrator or end user, you should be much to learn from the experience of past attacks (although the attack it happened to anyone else) to avoid the next attack will happen.
Knowing the type of attack is very important to maintain system stability, so you do not need bother to install a new system to make it more secure, you just need to patch or even a little Maybe configure your system for some of this paper is written very fundamental, but it would not hurt if you as a professional to review something basis from time to time .. This article is not intended to attack but instead is to survive, because it seems to me to survive you have to know how to attack.
In this article there are frequent attacks by crackers and every attack has methods separately, for example, only in doing IP spoofing method which has many of them man in the middle attack. With the above reasons I will try illustrates the exaggerated attacks.general is often done cracker and should be known by an Administrator or end user, while the methods may be more specific I pour in my writing whether the next attack or method in place to survive. I know the following article is far from perfect, for the suggestions and criticisms so I would expect.
1. IP SpoofingIP Spoofing is also known as the Source Address Spoofing, namely forgery attacker's IP address so that attacker considers the target IP address is the IP address of the host in the network rather than from outside the network. Suppose the attacker has a type A 66.25.xx.xx IP address when the attacker did This type of attack the network that attacked the attacker will assume the IP is part of the Network 192.xx.xx.xx eg, IP-type C. IP spoofing occurs when an attacker 'outsmart' packet routing to change the direction of the data or transmissions to different destinations. Packet to routing is usually transmitted in a transparent and clear so as to make the attacker to easily to modify the data origin or destination of data. This technique is not only used by the attacker but also used by security professionals to download Tracing the identity of the attacker.
Protocol that handles communication between computers most successful in the spoof. ICMP (Internet Control Message Protocol) is one of them (vulnerable) because the protocol is bypassed by the information and error messages between two nodes in the network. Internet Group Message Protocol (IGMP) can be exploited by using this type of attack because the IGMP report error conditions at the level of user datagram, but it also contains routing information protocol and Information Network. (UDP) User Datagram Protocol can also be 'asked' to display the identity of the target host. Solutions to prevent IP spoofing is a way to secure packet-packet is transmitted and installing screening policies. Encryption Point-to-point can also prevent users who do not have the right to read the data / packet. Authentication can also be used to filter the source legal and not a source that has been in the spoof by attackers. In another prevention, Admininistrator can use the signature for packages that communicate in network thus assured that the package is not modified in transit. Anti Spoofing rules (anti-spoof rules) which basically tells the server to reject packet is coming from outside the visible coming from the inside, generally this will break any spoofing attacks.
2. FTP Attack
One of the attacks carried out against the File Transfer Protocol is a buffer overflow attack caused by a malformed command. destination FTP server to attack this average is to get a command shell or to perform Denial of Service. Denial Of Service attacks may eventually lead to a user or attacker to take resource in the network without authorization, while the command shell can make a attacker gain access to the server system and data files that an attacker can eventually made anonymous-root acces that have full rights to the system even network was attacked. Never or rarely update the server version and patch to its, is a mistake that is often performed by an admin and this is what makes the FTP server to be prone to enter. An example is the popular FTP servers on the UNIX family of wu-ftpd which is always in upgrade two times a day to improve the conditions that permit the occurrence bufferoverflow FTP exploit also useful to know the password contained in the system, FTP Bounce attack (using ftp servers other people to carry out attacks), and knowing or mensniff information residing in the system.
3. Finger Unix Exploits
In the early days of the Internet, Unix OS finger efficient utility used to download information sharing among users. Due to requests for information on this finger information is not to blame regulations, many system administrators leave this utility (finger) with security very minimal, even with no security at all. For an attacker utility is extremely valuable for make information on footprinting, including login names and contact information. This utility also provide excellent information about user activity within the system, how long users are in the system and how much users care system. Information generated from this finger to minimize effort in penetrating a cracker the system. Personal information about users who raised the finger daemon is already sufficient for a atacker to perform social engineering by using social skill to utilizing a user to 'tell' passwords and access codes to the system.
4. Flooding & Broadcasting
An attacker could reduce the speed of networks and hosts that are in it are significant by continuing to perform request / demand any information from servers that can handle the classic attack Denial of service (Dos), send a request to a port in excess called flooding, sometimes this is also called spraying. When a request is sent to all flood stations that are in this attack dinamakn broadcasting network. The purpose of this second attack is the same that is making network resource that provides information becomes weak and finally give up. Attacks by flooding depends on two factors: the size and / or volume (size and / or volume). An attacker can cause Denial Of Service by throwing capacity files big or large volumes of small packets to a system. In such circumstances network server will face congestion: too much information requested and not enough power to push the data to run. Basically a big package requires the capacity the larger the process, but it is not normal and the same small package in a large volume will spend the resources in vain, and the resulting congestion.
Attackers often use these flooding attacks to gain access to the system used to attack other networks in an attack called Distributed Denial Of Service (DDOS). This attack is often called smurf if sent channeled through ICMP and called fraggles when this attack dijalakan through UDP. A node (used as tools) which amplifies the broadcast traffic is often referred to as Smurf Amplifiers, These tools are very effective to run the flooding attack. By doing the spoofing of target network, an attacker can send a request to the smurf amplifier, which in the Network amplifiying (amplified) will send a response kesetiap hosts in the network itself, which means a request made by the attacker will produce the same job and repetitive on the target network, the
Result of this attack is a denial of service that does not leave footprint. This attack can be anticipated by refusing to broadcast which is directed at the router. Flooding-level TCP (SYN ATTACK mostly) have been used in February 2000 to attacked Yahoo!, eBay, etc. that use DDOS attack (Distributed Denial Of Service).
Networks that do not use a firewall to check TCP packets can usually be attacked in this way. Some of the functions of filtering on the firewall (Firewall Filtering Function) will usually be able to withstand a flooding attack from an IP address, but the attack made by DDOS will be difficult to be prevented because of this attack as we know it came from a variety of IP addresses Periodically. Actually, one way to stop DDOS attacks is to return the package to the address of origin or also by turning off the network (usually done by systems that have been exposed to very severe attack).
5. Fragmented Packet Attacks
Internet data is transmitted via TCP / IP can be divided into packages that are only The first package contains the contents of which contains information on the main part (head) of the TCP. Some firewall will allow to process part of packages that do not contain information source address on the package first, this will result in some type of system to crash.
For example, the NT server will be a crash if the packets are broken up (fragmented packet) is enough to rewrite the first packet of information from a protocol. Packages which are broken down can also result in an atmosphere such as flooding attacks. Because the package split will remain stored until finally in the form back to the data is intact, the server will store the packets are broken up earlier in the kernel memory. And finally the server will be a crash if too many packages that have been broken down and stored in memory without re-united.
By way of enumeration of topographi target network, an attacker can have many option to either crash the packet by examining the contents of firewalls, load balancers or content - based routers. By not taking this defense system, the target network is much more prone to vandalism and burglary.
Because the packets are broken up (fragmented packet) is not recorded in the log file before it put back together the data is intact, the packet is split provides a way for hackers to get into network without the detection. There have been many Intrusion Detection System (IDS) and firewalls filter (firewall filters) to fix this problem, but still many systems that can still be penetrated by this.
6. E-mail Exploits
Peng-exploitasian e-mail occurs in five forms namely: Floods mail, manipulation command (command manipulation), the attack rate of transport (transport-level attack), enter the various codes (Inserting malicious code) and social engineering (utilizing socialization physically). Email attack can cause the system to crash, open and rewrite even execute files also make an application or access to command functions (command function). Attacks mail floods (flood = flood) occurs when large numbers of e-mail sent by the attacker to the target resulting in the transfer agent to handle overwhelmed, resulting in communication among other programs become unstable and can cause the system to crash. Doing flooding is a very crude but effective, means to create a mail server to be down. One interesting way of doing mail-flooding attack is to exploit the auto-responder (auto-responder function) found in most applications email, when an attacker to find an auto-responder is currently active in the two systems different, the attacker could redirect one to the other, because both are in the set to respond to sacara automatically to each message, then both will continue to mengenarate more e-mails in a loop (back and forth) and finally both be tired and down. Manipulating attack command (command manipulation attack) can result in a system a crash with a way to overthrow the mail transfer agent with a buffer overflow caused by commands (functions) are disabled (example: expn or VRFY). The difference between the mail flood and manipulation command: command manipulation to exploit the power belongs to send mail allow an attacker to access the system without the authorization information (the network admin unnoticed) and make other modifications to the run of the program. Enable command defective as above can also result in an attacker to access mendapatlan modify files, rewrite, and of course it makes trojan horses on the mail server.
Degree assault transport (transport-level attack) done in a way mengexploit-protocol router an / mapping across the internet e-mail: tranport Simple Mail Protocol (SMTP). An attacker can result in an error condition while (temporary error) in the target system in a way mengoverload more data on the SMTP SMTP buffer so the buffer can not handle it, the incident This can result in an attacker knocked out of the sendmail program and entered into the shell with power adminitsrasi can even take over the root. Some attacks also exploitable
common in POP and IMAP. At the moment it is difficult for SMTP vulnerability exploitable, the attacker may move to attack tranport level if he does not successfully attack by manipulation or mail-command flood. This attack is more used to create a disturbance rather than to break a system. A attacker would normally use to make flood type attacks Exchange Server and cut e-mail traffic (e-mail traffic). This attack can also be used to make the reputation of a organizations are becoming worse by sending spam or offensive e-mails to other organizations with source and the address of the organization.
Mail relaying, the process of falsifying the origin / source email by meroutekannya at the machine that will lied to, is another type of transport-level attacks. This technique is very useful for making broadcasting spam anonymously. Various kinds of content (content) are often sent via e-mail with this technique is usually a content-content that is damaging. Some Viruses and Worms will included in the e-mail as legitimate file attachments, such as Melissa variant that appears as Ms Word Macro or Loveletter worm that infects the system and mengemailkan itself to users who are in the address booknya outlook. Most antivirus scanners will capture attachment like this, but visrus and new worm and its variants are still dangerous. The last attack carried out by an attacker in addition to the above attack is by way of do social enginering, sometimes the attacker sends e-mails with a source address using users send the admin password in order to upgrade the system.
7. DNS and BIND Vulnerabilities
Recent news about the vulnerability (vulnerabilities) of the Berkeley Internet Name Domain applicationm(BIND) in various versions illustrate the fragility of the Domain Name System (DNS), namely the crisis directed at the basic operation of the Internet (Internet basic operation). Errors on BIND is actually not something new. Since permulaanya, standard BIND is the most favorite target for attack by a cracker community as some kerawanannya. Four vulnerability to buffer overflow that occurred in January and then only some parts of the vulnerability to diexploitasi by the cracker to get access to system and perform the command with full privileges (privilege command execution). Vulnerability in BIND is a very serious problem because more than 80 percent of the DNS Jagat was in the Internet built using BIND. Without the DNS in the Internet environment Modern, e-mail transmission may be difficult, navigating to web sites was complicated and may not there are other easy thing about the internet.
BIND vulnerability lies not only in the DNS. System address translators (number-address translator) is the subject of many exploits, including to carry out attacks in the information, Denial Of Service attack, the takeover of power by hijacking. The attack at the level of information is intended to make the server to answer something other than the correct answer. One way to do this type of attack is through cache poisoning, which will fool the remote name server to store the response from third-party domain by providing a wide range of information to the domain server that has the authorization. All of the implementation of the attack on DNS will have most likely to succeed done if the answer to a question that spesisfik be fooled (spoof). DOS or make the server could not operate, can be done by creating a DNS attack itself or also by sending excessive traffic-flooding from the outside, for example use "Smurf" ICMP flood. If an organization or company installed authoritathive name server in one segment that lies behind a link or behind a physical area,
then this will lead to a possibility to do Denial Of Service attacks. Cracker will try to attack the system via DNS by buffer overflow, which is one one partner has the potential to exploit the vulnerabilities of BIND. Disorders due to exploits weaknesses in the coding / programming BIND which allows an attacker to utilize code-code that can be executed to get into the system. Some operating systems has provided a patch for the stack that can not be executed, as well as conducted compiler (providing patches) that protect the stack from overflow. The mechanism of this protection stidaknya make the cracker would be difficult to use the exploit.
It is clear that updating the system regularly and use a patch is one that should be done to build effective security, if the vendor of your DNS does not provide patches on a regular basis, you better change your DNS software that provides patches in Periodically, of course, to maintain system security. On a Unix system, BIND must run as root to set a lower port (kodekode machine). If the DNS software can be fooled to run code-malicious code, or open files owned by root, a local user may be able to increase his own power in the machine. Organization or company that transforms authoritative servers should also be aware that replacing
their servers at the same time will result in the hijack their domains through the cache poisoning. Changing the server should be done as the transition process. To prevent domain hijacking network admin should first menambahkn new server into the network Infrastructure before replacing the old server.
8. Password Attacks
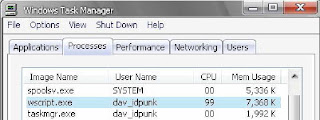
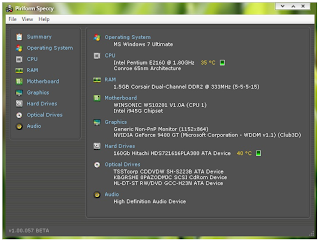
Password is a common thing when we talk about security. Sometimes a user does not concerned with the pin number that they have, such as online transaction in the cafe, even transact online at home is also very dangerous if not equipped with security software such as SSL and PGP. Password security is one procedure that is very difficult to attack, an attacker may Just have lots of tools (technically as well as in social life) only to open something that is protected by a password. When an attacker managed to get a password owned by a user, then he will have power equal to that user. Train employees / users to remain vigilant in safeguarding the password of social engineering can at least minimize risk, but in case of social enginering practices organizations must also be wary this is a technical way. Kebnayakan seranagn committed against the password is guessed (Guessing), brute force, cracking and sniffing. Guessing (guessing) the password can be done by entering the passwords one by one in bantuin manually or with scripts that have been programmed. Most users use things that public for their password including date of birth, and usually the user is not worrying about rules that apply to the company to use a combination of alphanumeric and at least 7 character. If only the user using his date of birth as the password then this attack will be very easy to do, because the cracker does not require a long time just to break down the 6 digit digit date of birth. Some of the user or even administrator can make the job a cracker easier if only they forgot to change the default password of a software.
Actually, password guessing is something that is not very effective, and can spend time. Network admins can easily detect the attack if an attacker trying to login by guessing the password frequently. Brute-force attack that uses the logic is the same with password guessing, but brute-force attack faster and more powerful. In this type of attack an attacker using a script (usually free cracking programs) that will try passwords general (usually found in the dictionary). The purpose of this type of attack is to accelerate discovery before the network admin password is aware of the attack. Although the Brute-force attack is more efficient than guessing passwords, these two techniques on essentially the same. Attacker is generally more difficult to succeed with both these methods. Further Again, both techniques are very easy on the opponent by using blacklisting features, which will lock a user account if someone (the attacker) repeatedly enter passwords are not the right. For example, the default blacklist in unix system is three times (the chance to enter password).
The weakness of the protection feature blacklist blacklist is that it can igunkan to attack system by the attacker. For example, if an attacker can identify who the login name for network administrator, the attacker could have save a login name and password to enter the one repeatedly and finaly lock the admin account ☺. When the admin is trying to get access back, an attacker is still able to relate to the system. Password cracking is a method for protection against the encrypted passwords in the system. Assuming that atacker been entered into the system, he could have changed power within the system with a way to crack the password file using brute-force method dictionary attack (match the words in the dictionary with words that are encrypted in the password file). The success of using this method depends on processor speed and programs that are owned by the attacker. The best way to avoid this type of attack is with the authority to monitor access to the file. By way of peering traffic on port telnet (23) or HTTPD (80), an attacker can
get a password that is used to remotely connect the internet and through a process snifing called password. The easiest way to do this is because the second connection do not use encryption, except for connections that use SSL (secure socket layer) on HTTPD (usually under the browser locked padlock sign, which indicates a secure transaction) or also use SSH (Secure Shell) to connect to other machines remotely.
9.Proxy Server Attacks
One function is a proxy server to speed up response time by way of uniting process of multiple hosts in a trusted network. In most cases, each host has power to read and write (read / write) which means what can I do in the system I'll I can also do in your system and vice versa. If the firewall that is in the trusted network is not configured optimally, particularly for block access from outside, especially if the authentication and encryption is not used, an attacker can attack the proxy server and get the same access to other members of the trusted network. If attaker been entered into the system he certainly could do anything and he can do DDOS (distributed denial of service) are anoymous to attack other networks.
The router is not configured optimally also will serve as a proxy server and will vulnerability to the same result with a proxy server.
10. Command Processing Remote Attacks
Trusted Relationship between two or more hosts provide exchange of information and resource facility sharing. Similar to a proxy server, trusted relationship provides to all members network access to the same power at one and the other system (the network). Attacker will attack the servers that are members of the trusted system. Just as vulnerability on the proxy server, when access is received, an attacker would have the ability to execute commands and access the data available to other users.
11. Remote File System Attack
Protocols for data transport backbone of the Internet-is the level of TCP (TCPLevel) with a mechanism that has the ability to read / write (read / write) between network and hosts. Attacker can easily get trace information from this mechanism to gain access to the directory file. Depending on the OS (operating system) is used, the attacker could extrack information about network, sharing privileges, the name and location of users and groups, and the specification of the application or banner (name and version of software). System is configured or secured to a bare minimum will easily expose this information through the firewall even though. On UNIX systems, This information was taken by the NFS (Network File System) on port 2049. Windows systems provide data is the SMB (server messaging block) and on port netbios 135-139 (NT) and port 445 on win2k. Network administrators can minimize the risk that would occur by using Protokolprotokol by providing them with little regulation. Network with Windows systems, should block access to ports 139 and 445 from outside the network, if possible. In 2049 the port unix system should be in block, file sharing is limited and requests the file through the showmount (command in unix) should be noted in the log.
12. Selective Program Insertions
Selective Program Insertions are done when the attacker attacks that put the programs crushers, such as viruses, worms and trojans (you probably already know this term well ☺) on the target system. These programs are often also called the destroyer of malware. These programs are have the ability to damage the system, destruction of files, stealing passwords up to open the backdoor. Usually sold in the market will antivirus can detect and clean up programs like this, but if there is a new virus (just think of melissa variant) virus scanner may not be face the new scripts. Some network administrators perform defense against malware
with alternative technologies such as behavior blockers, which lay off the codes that are suspected based on the behavior of malware examples, not by signature. Some other applications will be quarantine the virus and code-code that is suspected in a protected area, usually called sandboxes.
13. Port Scanning
Through port scanning an attacker can see the function and how to survive a system of various kinds of ports. A atacker can get access to the system through an unprotected port. Sebaia example, scanning can be used to determine where the default SNMP string in the open for public, which means information can be extracted for use in remote command attack. Sequence
14. TCP/IP stealing, Passive Listening Port and Packet Interception
TCP / IP Sequence stealing, Passive Listening Port and Packet Interception runs to collect sensitive information to access the network. Unlike active attack or brute-force, attacks using this method has more stealth-like qualities.
TCP / IP Sequence stealing is a mapping from the sequence of numbers (digits), which could make a packet attacker's look legal. When the system asks the session on another machine, the two systems are exchanging TCP synchronization numbers. If not done at random, the attacker can recognize algorithm used to generate these numbers. Sequence of numbers that have been stolen can Attackers used to impersonate one of the earlier system, and finally allow it to pass through the firewall. It is actually effective when used with IP Spoofing.
Through passive listening ports, an attacker can monitor and record (log) of all messages and files sent to all ports that can be accessed on the target system to find the point of vulnerability. Packet Interception is the (exact coating) of the active listener on port programs that are in target system or restore functions to receive all types of messages (data) specific is sent. Such messages could be returned to the unauthorized systems, and its final reading returned either no change or even with the changes to the attacker, or even not is returned.
In some versions or also according to the configuration of the user SSHD (secured shell daemon), authentication can be done by using the public key (owned by machine of course). If an attacker learn the public key is used, it can create or insert false packets. System target will assume the sender is spoofed packets have access rights.
15. HTTPD Attacks
Vulnerabilities contained in the HTTPD webserver or there are five kinds: buffer overflows, httpd bypasses, cross scripting, web code vulnerabilities, and URL Floods. HTTPD buffer overflow can occur because the attacker to add errors to the ports used for web traffic by entering the lot carackter and strings to find a place
corresponding overflow. When a place is found for the overflow, an attacker would enter string that will be a command that can be executed. Buffer-overflow can give the attacker access to the command prompt.
Several of the HTTPD feature can be used to meciptakan HTTPD byapass, giving access to server using the logging function. In this way, a web page can be accessed and replaced without recorded by the web server. This method is often used by the cracker, and cyber hacktivis Vandals to defacing a website. While vulnerabilities in web scripts can happen to all web programming languages and all extension applications. Including VB, Visual C + +, ASP, TCL, Perl, PHP, XML, CGI and Coldfusion. Basically, the attacker will exploit the weaknesses of an application, such as CGI scripts not check the input or the IIS RDS vulnerability that allows running on showcode.asp commands remotely (remote command priviledges). Through cross-scripting and cross-site scripting an attacker could exploit the exchange of cookies between browser and webserver. This facility could enable the script to change the look of the web, etc..
This script can be run malware, read important information and to expose sensitive data such as credit card number and password. In the end, the attacker can run a denial of service with the URL flood, which is done by how to repeat and keep repeating the request to port 80 via httpd are the limits TTL (time to live). Some of the user or manager may hate to hear these attacks. But on fact is nobody really fix to secure the network or website. Security is a process, not product. If you install a firewall, IDSes (instrusion detection system), routers and honeypots (system to trap) may be able to provide the layers to survive, but once again the most advanced equipment in the world will not help an organization until the organization has a process to upgrade the system, wear the patch, check security on the system itself and other methods. There have been many companies that use IDSes but does not monitor log files, they installed firewall, but not the upgrades. The best way to protect a website or network of attack is intended to bring security challenges as going against safety
itself, keep trying, always remember the basics and do not forget to pray ...:)
May be Helpful ^_^
Types of Cracker Attacks and its Prevention
 4:55 AM
4:55 AM
 indigo
indigo